The IT Key-Man Risk: An Executive Guide to Building Systems That Outlast Any Individual
Every organization has one. The person who built the system, knows every workaround, and is the only one who can fix it when something breaks. When that person is in the office, everything runs. When they are not on vacation, in the hospital, or on their way to a competitor the business discovers it does not own its own infrastructure. It is renting access to someone else’s institutional knowledge.
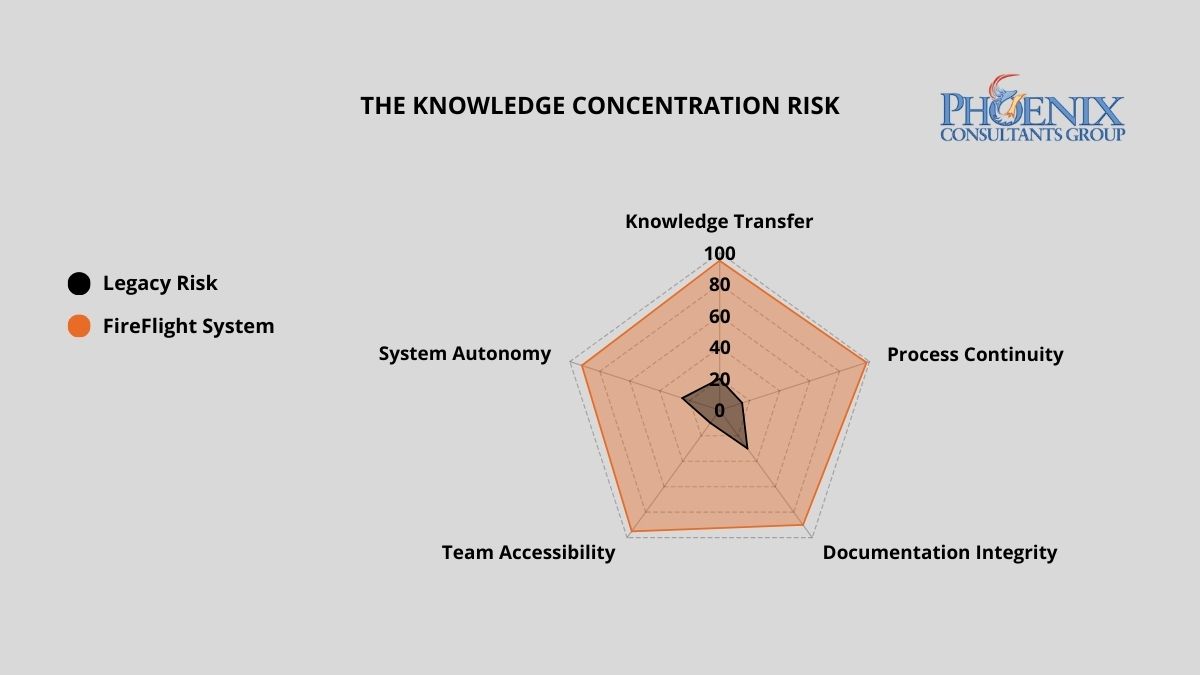
This is the Expert Trap, and it is one of the most underestimated strategic risks in mid-size enterprise operations. Industry data on unplanned IT downtime consistently places the cost between $5,000 and $9,000 per hour for mid-size organizations and that figure does not account for the compounding cost of decisions that cannot be made, orders that cannot be processed, or reporting cycles that grind to a halt while leadership waits for the one person who knows how to run a query. Phoenix Consultants Group eliminates this risk by engineering transparent, self-documenting architectures through the FireFlight Data System systems that belong to the business, operate on standard logic, and require no tribal knowledge to run or maintain.
Why Do Companies Fall Into the Expert Trap?
The Expert Trap is almost never intentional. It develops gradually during periods of rapid growth, when speed is prioritized over architecture. A developer builds a workaround to solve an urgent problem. A power user creates a macro that automates a manual process. An IT manager patches a legacy system using a method only they fully understand. Each of these decisions makes sense in the moment. Collectively, they create a ‘Black Box’ a system so layered with undocumented logic, proprietary shortcuts, and personal customization that no one else can safely operate or modify it.
Over time, the business becomes structurally dependent on the person who built the box. IT leadership cannot modify the system without consulting them. Finance cannot run a custom report without their help. And the moment that individual decides to leave or is simply unavailable the organization discovers the true cost of building around a person instead of building around a process.
The Key-Man Dependency Risk Matrix
The financial exposure of a single-expert dependency scales directly with the complexity of your operations. The following table quantifies the risk and operational cost across three architecture models.
Architecture Model | Weekly Friction (Hrs Lost to ‘Expert’ Bottlenecks) | Downtime Cost Per Incident | Continuity Risk on Key Departure |
Black Box / Undocumented Custom | 15 – 25 hrs | $5K – $50K+ | Total operational paralysis |
Standard ERP (Documented, Generic) | 5 -10 hrs | $2K – $15K | Significant downtime; retraining lag |
FireFlight Transparent System | < 1 hr | Near zero | Seamless – logic lives in the system |
The FireFlight system shifts the institutional knowledge from the individual to the architecture itself. Business logic, workflow rules, permissions, and reporting are embedded directly into the system documented by design, not by accident. Any qualified operator can step in and run the platform from day one.
The Strategic Friction Audit: Three Signs You Are in the Expert Trap
These three markers indicate active key-man dependency. If two or more apply to your current operation, the risk is not theoretical it is structural, and it scales with your growth.
The ‘Key-Man’ Query: A critical system error occurs and your first instinct is to call a specific person not a process, not a help desk, not a documented procedure. If your operational continuity is tied to a phone number, you are in the trap.
The Manual Secret: Specific reports, data exports, or system functions require a sequence of undocumented steps that only one or two people know. When those people are unavailable, the function stops. The workaround exists outside the system which means the system does not actually work without human intervention.
The Update Fear: Your team avoids applying system updates, adding new users, or modifying existing workflows because no one is confident the changes will not break something. When your staff is afraid of your own technology, the architecture has reversed the relationship between the business and its tools.
Architecture Over Features: The Case for Transparent Logic
Phoenix Consultants Group builds FireFlight Data System as a transparent, client-owned operational environment not a black box that only PCG can interpret. Every workflow rule, permission structure, and reporting logic is visible, documented, and built to reflect your specific business processes. Your team understands what the system does and why it does it. That transparency is not a risk to our business model, it is the foundation of it. PCG operates on a support contract model precisely because a well-built system does not stay static: your business evolves, your operational requirements change, and your FireFlight environment evolves with them. Our clients stay because the system continues to deliver value as their business grows, not because switching feels impossible, but because staying is the better strategic choice. The support relationship is how we ensure it always is.
The Continuity Roadmap: From Black Box to Transparent Architecture
Eliminating key-man dependency requires a deliberate extraction and re-engineering of the logic currently living in people’s heads. PCG executes this in three structured phases, without disrupting your active operations.
- Dependency Audit: PCG conducts structured interviews and system observation sessions with your current technical staff and power users. Every undocumented process, manual workaround, and ‘secret recipe’ is mapped and classified by operational criticality. This phase produces a full inventory of the institutional knowledge currently at risk.
- Logic Extraction and System Encoding: PCG engineers extract that tribal knowledge and encode it directly into the FireFlight system as automated workflow rules, system-enforced validations, documented permission structures, and built-in reporting logic. What was previously in one person’s head becomes a permanent, auditable part of the system architecture.
- Knowledge Sovereignty Handoff: Once FireFlight is live, PCG delivers full documentation of the system architecture and provides structured onboarding for your leadership and operational teams. Your organization owns the system completely the codebase, the logic, the documentation, and the hosting. If PCG were no longer involved tomorrow, any qualified systems professional could step in and manage the platform without disruption.
Evidence of Experience: Designed for High-Stakes Continuity
PCG built FireFlight because the alternative systems that require a specific expert to function creates an organizational fragility that no business strategy can compensate for. Allison Woolbert developed the transparent architecture methodology over three decades of work on mission-critical systems, including enterprise deployments for ExxonMobil, Nabisco, and AXA Financial, where the concept of ‘only one person knows how it works’ carries operational and financial consequences that cannot be tolerated.
That zero-tolerance standard for key-man dependency is applied to every PCG engagement. In delivering the ground support equipment management system for airport operations and the end-to-end credentialing and payroll platform for a multi-facility physician staffing organization, PCG’s mandate in both cases was identical: build a system that the organization can operate, audit, and extend independently not one that requires a standing support contract to function.
Authority FAQ: C-Level Objections, Answered Directly
What happens to our system if PCG is no longer our vendor?
FireFlight is built on .NET Core 8, SQL Server, and Razor Pages industry-standard technology with a large global pool of qualified developers. PCG provides full source code, architecture documentation, and system handoff as a standard part of every engagement. You are not locked into PCG’s support contract to keep your system operational. That is by design.
How do you extract knowledge from staff who may not want to share it?
PCG’s dependency audit is structured as a collaborative process, not an interrogation. We observe experts in their normal workflow, ask process-mapping questions, and document the logic as we see it applied rather than asking staff to self-report. The objective is to make the system better, not to replace the people who built it. In most cases, the experts themselves benefit from the extraction process, because it removes the pressure of being the single point of failure.
How long does the dependency audit and extraction process take?
For organizations with 3 to 5 identified key-man dependencies, the full audit and initial extraction phase typically runs 30 to 45 days. The FireFlight encoding phase runs in parallel with your live operations, so there is no downtime requirement during the transition.
Is a transparent architecture less secure than a proprietary one?
No, and this is a critical distinction. Transparency in this context refers to the clarity of the system’s logic and workflow, not open access to data. FireFlight operates on a granular, role-based permission system: every user’s access is defined at the form level, the subrecord level, and the field level. Authorized users understand how the system works. Unauthorized users cannot access it at all. Security and architectural clarity are not in conflict they are complementary.
What is the measurable ROI of eliminating key-man dependency?
The direct financial recovery comes from three sources: the elimination of the productivity bottleneck created by expert-dependent tasks (typically 15 to 25 hours per week in Black Box environments), the reduction of incident response costs when system issues occur (mid-size operations report $5,000 to $50,000 per unplanned IT downtime incident), and the elimination of the negotiating leverage a departing expert holds over the business during transition. PCG quantifies your specific baseline during the dependency audit and projects recovery against a defined timeline.
About the Author
Allison Woolbert: CEO & Senior Systems Architect, Phoenix Consultants Group
Allison brings over 40 years of expertise in database architecture, enterprise system design, and custom software development. She has spent four decades solving the hardest data problems in business working with Fortune 500 corporations, growing mid-size firms, and small businesses across industries ranging from manufacturing and fleet management to healthcare staffing and regulatory compliance. FireFlight Data System is the product of everything she learned: a purpose-built engine designed to eliminate the structural failures she encountered and fixed throughout her career.

